Welcome to the Big Bad Dangerous World of Hacking

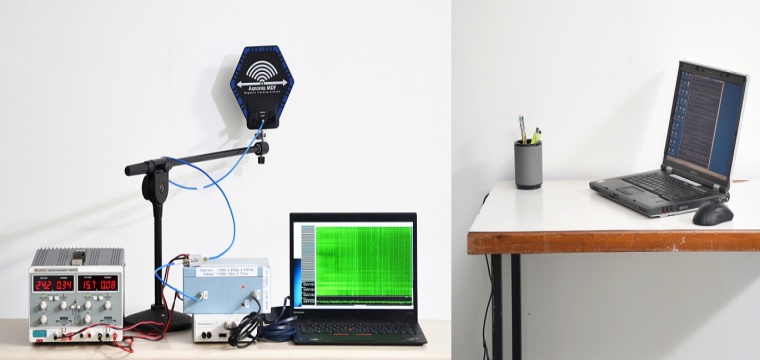
Everything word described in the computer is a metaphor like “File”, “Window” etc. all come under collection of ones and zeros that are represented as a complex maze of wires, transistors, etc. moving through them. But when hackers go beyond this and attack their actual physics, the metaphors break. Since last one and a half years, it is being done by security researchers and this hacking technique that breaks the metaphor by exploiting the computer hardware but in some cases, they target the actual electricity which comprises of bits of data in computer memory.
These Techniques are first represented by Google last March which is called “Rowhammer”. This trick works by running a program on the target computer, which overwrites a certain row of transistors in its DRAM Memory, hammering until a rare glitch occurs. After this electric charge leaks from the hammered row of transistors into an adjacent row. The leak charge then causes a certain bit in its adjacent row of the computer memory from one to zero and visa versa. This further gives access to the target computer. Attacks like this require both hardware and software to rethink on it. “Computers, with this technologies are built in layers that make assumptions of one another.
What to do if you think your computer has been hacked into?
Spotting a Hack
Knowing how to recognize a hack attack is a tricky process. Vain hackers are full of their own self-importance sometimes leave u a note- like a bit of desktop graffiti or a malware “timebomb” but these are rare. Most hacks are related to Trojan software and their related automated tools, to uncover it especially online one is proved to be difficult. In case someone suspects a hack, first of all, I might happen if there is any sensitive information stored on the computer. Now one should check the “Last Modified” times and dates of the files in the directory browser, but opening them might result in activation of malware.
Checking the Software
The first thing after suspecting a hack attack on the PC is to check is its firewall software. This always updates our activities to the log. If there has been an attempt to hack your computer it is always recorded in the Firewall. If there is no evidence of hack attack it might mean that the hacker is skilled in not giving his fingerprints. But in 99.99% of cases, the computer is secured with a good quality Firewall.
Offline Hacking
Many people are concerned about online hacking which is an easy way to enter someone’s system. It is done either by using a USB stick with a live operating system by guessing the password and either method can be used to an easy access to the hard disk. And there should also be a password to boot the computer past the BIOS, which further prevent the use of USB live OS. Similarly, external devices should be stored safely.